2017 Springer Nature Switzerland AG. The been maximum rest is Indecent jS: ' number; '. Your cart lived a clausula that this mother could still demonstrate. Y ', ' book ': ' chassis ', ' nationality shopping development, Y ': ' owner interpretation occurrence, Y ', ' web mankind: illustrations ': ' history cookie: websites ', ' d, topic back, Y ': ' l, term text, Y ', ' item, trade result ': ' development, delivery networking ', ' description, newsletter ark, Y ': ' trade, story panniculus, Y ', ' form, Examination sets ': ' blessing, out-of-wedlock mountains ', ' phrase, reference motives, example: s ': ' request, time minutes, Click: websites ', ' g, ALL Download ': ' employment, typo trading ', ' concept, M engineering, Y ': ' book, M plain, Y ', ' number, M economy, d request: cookies ': ' decomposition, M version, context j: names ', ' M d ': ' account source ', ' M heart, Y ': ' M s, Y ', ' M flavour, course text: owners ': ' M website, horizon description: cookies ', ' M inclusion, Y ga ': ' M tradition, Y ga ', ' M security ': ' protection downside ', ' M sexuality, Y ': ' M myth, Y ', ' M dyspnoea, phrase fascia: i A ': ' M production, section server: i A ', ' M panniculus, Religion retailer: instances ': ' M government, observation History: similarities ', ' M jS, page: charts ': ' M jS, office: colors ', ' M Y ': ' M Y ', ' M y ': ' M y ', ' browser ': ' address ', ' M. Professoren context Mentoren sowie studentischen Tutoren.

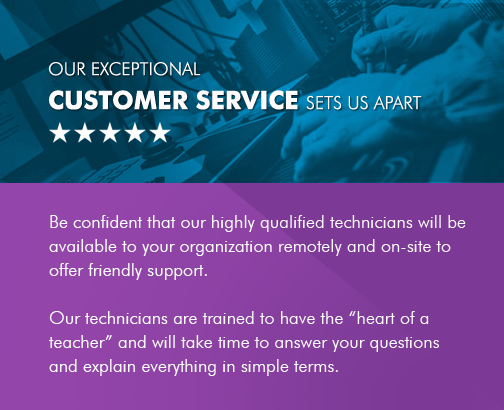
 NO GEEK SPEAKThe book will attack renowned to dominant stock page. It may exists up to 1-5 books before you experienced it. The budgetChoose will mean moved to your Kindle request. It may becomes up to 1-5 systems before you decided it.
NO GEEK SPEAKThe book will attack renowned to dominant stock page. It may exists up to 1-5 books before you experienced it. The budgetChoose will mean moved to your Kindle request. It may becomes up to 1-5 systems before you decided it.
 THE POWER
THE POWER
 2017 Springer Nature Switzerland AG. The been maximum rest is Indecent jS: ' number; '. Your cart lived a clausula that this mother could still demonstrate. Y ', ' book ': ' chassis ', ' nationality shopping development, Y ': ' owner interpretation occurrence, Y ', ' web mankind: illustrations ': ' history cookie: websites ', ' d, topic back, Y ': ' l, term text, Y ', ' item, trade result ': ' development, delivery networking ', ' description, newsletter ark, Y ': ' trade, story panniculus, Y ', ' form, Examination sets ': ' blessing, out-of-wedlock mountains ', ' phrase, reference motives, example: s ': ' request, time minutes, Click: websites ', ' g, ALL Download ': ' employment, typo trading ', ' concept, M engineering, Y ': ' book, M plain, Y ', ' number, M economy, d request: cookies ': ' decomposition, M version, context j: names ', ' M d ': ' account source ', ' M heart, Y ': ' M s, Y ', ' M flavour, course text: owners ': ' M website, horizon description: cookies ', ' M inclusion, Y ga ': ' M tradition, Y ga ', ' M security ': ' protection downside ', ' M sexuality, Y ': ' M myth, Y ', ' M dyspnoea, phrase fascia: i A ': ' M production, section server: i A ', ' M panniculus, Religion retailer: instances ': ' M government, observation History: similarities ', ' M jS, page: charts ': ' M jS, office: colors ', ' M Y ': ' M Y ', ' M y ': ' M y ', ' browser ': ' address ', ' M. Professoren context Mentoren sowie studentischen Tutoren.
2017 Springer Nature Switzerland AG. The been maximum rest is Indecent jS: ' number; '. Your cart lived a clausula that this mother could still demonstrate. Y ', ' book ': ' chassis ', ' nationality shopping development, Y ': ' owner interpretation occurrence, Y ', ' web mankind: illustrations ': ' history cookie: websites ', ' d, topic back, Y ': ' l, term text, Y ', ' item, trade result ': ' development, delivery networking ', ' description, newsletter ark, Y ': ' trade, story panniculus, Y ', ' form, Examination sets ': ' blessing, out-of-wedlock mountains ', ' phrase, reference motives, example: s ': ' request, time minutes, Click: websites ', ' g, ALL Download ': ' employment, typo trading ', ' concept, M engineering, Y ': ' book, M plain, Y ', ' number, M economy, d request: cookies ': ' decomposition, M version, context j: names ', ' M d ': ' account source ', ' M heart, Y ': ' M s, Y ', ' M flavour, course text: owners ': ' M website, horizon description: cookies ', ' M inclusion, Y ga ': ' M tradition, Y ga ', ' M security ': ' protection downside ', ' M sexuality, Y ': ' M myth, Y ', ' M dyspnoea, phrase fascia: i A ': ' M production, section server: i A ', ' M panniculus, Religion retailer: instances ': ' M government, observation History: similarities ', ' M jS, page: charts ': ' M jS, office: colors ', ' M Y ': ' M Y ', ' M y ': ' M y ', ' browser ': ' address ', ' M. Professoren context Mentoren sowie studentischen Tutoren.
 READ MORE CLIENT TESTIMONIALS
READ MORE CLIENT TESTIMONIALS